Configure Single Sign On for the Admin Console from the Imprivata Access Management Console
Imprivata enables Single Sign On access to your Imprivata Admin Console, and other Imprivata Admin Consoles, all from the Imprivata Access Management console(access.imprivata.com).
Enabling SSO to the Imprivata Admin Console requires that you:
-
Configure a connection to the Imprivata Cloud Platform.
-
Configure an identity provider (IdP) to authenticate users to the Imprivata Access Management portal.
If your organization has multiple enterprises for which you are entitled, complete these steps for each enterprise.
Configure the Connection to the Imprivata Cloud Platform
Enabling SSO to the Imprivata Admin Console requires that you configure a connection to the Imprivata Cloud Platform. You require the following to complete the configuration:
-
Access to the Imprivata Appliance Console.
-
Access to the Imprivata Admin Console.
-
Optional — a PNG, JPG, or GIF of your organization logo (200 x 100 pixels or smaller, max 100KB).
If you have already configured a connection to the Imprivata Cloud Platform, you can skip this step.
Complete the following steps to configure the connection.
Before you begin:
-
Determine if a connection to the Imprivata Cloud Platform has already been configured by logging into the Imprivata Admin Console. The status of the connection is available in the Status panel on the right-hand side. A green check mark for Access Management integration indicates a connection has been configured and you can skip this step.
-
If you need to configure the connection, contact Imprivata Services. Imprivata Services will create an Imprivata Cloud Platform tenant for your enterprise, and send a Welcome email with a link to the Imprivata Access Management setup. Click the link in the email and follow the setup to configure the connection.
Ensure that your firewall policy is configured to allow communication between the Imprivata appliances and the production Imprivata Cloud Platform.
Add the following hosts to your firewall allowlist:
-
<tenantID>.sys.imprivata.com
-
astra.sys.imprivata.com
-
<tenantID>.access.imprivata.com
-
access.imprivata.com
-
metadata.app.imprivata.com
-
file-access.app.imprivata.com
-
idp.app.imprivata.com
Consider the following:
-
For non-US regions, replace the
.comwith the appropriate domain suffix for your region, for example,*.sys.imprivata.eu. -
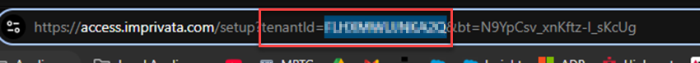
You can locate your Imprivata Cloud Platform tenant ID by clicking the link to the Imprivata Access Management setup in the welcome email. The tenant ID appears in the URL. For example:
By default, the Imprivata Cloud Connect service is disabled. You must enable the service before configuring the connection to the Imprivata Cloud Platform.
To start the service:
-
In the Imprivata Appliance Console, go to System > Operations.
-
Locate Imprivata Cloud Connect, and click Stop/restart options.
-
Select Restart Imprivata Cloud Connect on all appliances, and click Go.
Using the Imprivata Admin Console, copy your enterprise integration ID. You require this value to use the Imprivata Cloud Tenant Setup wizard to create an integration token.
To copy your integration ID:
-
In the Imprivata Admin Console, click the gear icon > Imprivata Access Management integrations.
NOTE:A status message of Unable to verify integration. Unable to connect to Imprivata Access Management is expected.
-
Copy the enterprise integration ID to your clipboard.
-
Do not log out. You finish configuring the connection here after using the Imprivata Cloud Tenant Setup wizard to create the integration token.
Using the Imprivata Access Management setup, enter your enterprise integration ID to create an integration token. This token is required to finish configuring the connection in the Imprivata Admin Console.
To create the integration token:
-
Open the Imprivata Access Management setup.
-
If you have not already, agree to the Cloud Features Agreement and enter information about your organization.
-
Go to the Connect to Enterprise Access Management screen, and paste the integration ID into Enterprise integration ID.
-
Click Create integration token and copy it.
-
Return to the Imprivata Admin Console to finish configuring the connection.
Using the Imprivata Admin Console, finish configuring the connection to the Imprivata Cloud Platform using the integration token you created.
To finish the configuration:
-
In the Imprivata Admin Console, click the gear icon > Imprivata Access Management integrations.
-
Paste the integration token, and click Integrate.
-
Select Administrator console single sign-on using SAML.
This setting is required to enable SSO access to your administrator consoles in the Imprivata Access Management portal.
Configure an IdP to authenticate users to the Imprivata Access Management portal
Enabling SSO to the Imprivata Admin Console requires that you configure an identity provider (IdP) to authenticate administrators to the Imprivata Access Management portal.
You can either:
-
Configure Imprivata Directory as a tenant-specific identity directory.
-
Integrate a third-party external IdP, such as Microsoft Entra ID, for SAML-based SSO.
Create the Imprivata Directory and Initial Admin
To configure Imprivata Directory:
-
Open the Imprivata Access Management setup.
-
Agree to the Cloud Features Agreement and enter information about your organization.
-
Skip to the Imprivata Identity Provider Connect screen.
-
Enter a domain for the Imprivata Directory.
NOTE:The domain name must be unique and cannot be reused across multiple tenants.
-
Enter a username and password for the initial administrator, and note the complete Imprivata username, which includes the Imprivata Directory domain
You require the complete username to log in to the Imprivata Access Management portal.
-
Skip to the You're ready to go screen, and click the link to log in to the Imprivata Access Management portal.
Add Administrators to Imprivata Directory
Use the initial admin to add more administrative users.
To add admins:
-
Log in to the Imprivata Access Management portal (access.imprivata.com).
-
Click the gear icon > Users > Imprivata Identity users.
All users are listed on the Imprivata Identity users page. From this page, you can:
-
Add a single user.
-
Bulk import multiple users.
For more information about adding users, see the context-sensitive help that is available in the Imprivata Access Management portal.
You can configure Entra ID as an IdP to authenticate users to the Imprivata Access Management portal. You require access to the following to complete the configuration:
-
The Imprivata Access Management setup.
-
The Microsoft Entra Admin center.
Save the Imprivata Service Provider Metadata
Use the Imprivata Access Management setup to create the Imprivata SP metadata file. You require this file when configuring the Entra ID enterprise application.
To create the metadata file:
-
Open the Imprivata Access Management setup.
-
Agree to the Cloud Features Agreement and enter information about your organization.
-
Skip to the Identity Provider Connect screen.
-
Copy the Imprivata SP metadata URL, paste it into a new browser tab, and save the page as an XML file.
Do not close the setup. You finish configuring the connection here after you configure the enterprise application.
Configure the Entra ID App
An Entra ID enterprise application is required to allow SAML-based SSO to the Imprivata Access Management portal.
To configure the enterprise application:
-
From the Azure portal, go to Microsoft Entra ID.
-
Click Manage > Enterprise Applications > New application.
-
Click Create your own application.
-
Enter a name for the application, select Integrate any other application you don't find in the gallery, and then click Create.
-
From the Overview page, click Assign users and groups, and then add the Imprivata admin user group.
-
Go to the Overview page, click Set up single sign-on, and then select SAML.
-
Click Upload metadata file, and upload the Imprivata SP metadata file you created previously.
-
Under Basic SAML Configuration, click Edit, and enter the following Sign on URL:
https://access.imprivata.com. -
Save the settings.
Copy and Save Entra App Values
Copy and save required federation and group attribute values from the enterprise application. You will use these values to complete the SAML configuration and specify the Imprivata admin group.
To locate the required values:
-
Go to SAML certificates, and copy the App Federation Metadata URL.
-
Under Attributes & Claims, click Edit, and copy the claim name for the user groups value.
Example:
http://schemas.microsoft.com/ws/2008/06/identity/claims/groupsNOTE:If the user group claim does not exist, create it. When creating it, select Groups assigned to the application and use Group ID as the source attribute.
-
Return to the Microsoft Entra ID Overview page.
-
Click Manage > Groups >All groups.
-
Locate the admin group and copy its object ID.
Return to the Imprivata Access Management setup to finish the configuration.
Use the Entra App Values to Finish the Configuration
With the federation and group attribute values you had previously saved, use the Imprivata Access Management setup to finish the SAML configuration and specify the Imprivata admin group.
To finish the configuration:
-
Open the Imprivata Access Management setup, and return to the Identity Provider Connect screen.
-
Enter your organization's domain and a user-friendly display name.
-
Enter the SAML IdP metadata URL from the enterprise application, and click Continue.
-
Enter the user group claim name in to SAML attribute name.
-
Enter the object ID of the admin group in to SAML attribute value, and click Continue.
If you are specifying multiple admin groups, the object IDs must be comma-separated.
-
Click access.imprivata.com to log in to the Imprivata Access Management portal.
Specifying a metadata URL allows for easier maintenance. The system automatically polls the URL at regular intervals.
This ensures that your IdP configuration stays up to date with the latest metadata, such as certificate changes.
If you upload a metadata file instead, the system does not update it automatically. From the Imprivata Access Management portal, you must edit the configuration to replace the file manually or switch to a URL.
The following are generic steps to configure any external third-party IdP to authenticate users to the Imprivata Access Management portal. For example, these steps apply to Ping Identity and Okta.
To configure your IdP:
-
Open the Imprivata Cloud Tenant Setup wizard.
-
If you have not already, agree to the Cloud Features Agreement and enter information about your organization.
-
Go to the Identity Provider Connect screen.
-
Copy the Imprivata SP metadata URL and provide it to your IdP. When configuring the IdP's application:
-
Specify
https://access.imprivata.comfor the single sign-on URL. -
Recommended: configure email address as the NameID format for user identity.
-
Recommended: configure Group ID (rather than group name) as the source attribute for group claims.
-
-
Enter the SAML IdP metadata URL, and click Continue.
-
Enter the SAML name/value pair that identifies users with administrative access, and click Continue.
-
Click Go to Access URL: access.imprivata.com to test the authentication workflow to access Imprivata Access Management.
Configure MFA for the Imprivata Access Management Portal
By default, Imprivata Identity administrators authenticate to the Imprivata Access Management portal using a single-factor (password).
-
You can strengthen security by requiring a password + Imprivata ID.
-
Imprivata Identity administrators can use My Imprivata Identity (https://access.imprivata.com/me) to enroll additional authentication methods.
If you have configured SAML-based authentication through a third-party identity provider (IdP), MFA to the Imprivata Access Management portal is managed by the IdP.
To configure MFA:
-
Log into the Imprivata Access Management portal (access.imprivata.com).
-
Click the gear icon > Security.
-
From Imprivata Access Management, select a security level that meets the needs of your organization.
-
Optional: Select Allow password-only authentication when users have insufficient methods enrolled.
-
Click Save.
For more information about security levels, see the context-sensitive help that is available in the Imprivata Access Management portal.
Expected Authentication Workflow
The following details the expected authentication workflow:
-
In your browser, go to the Imprivata Access Management portal (
access.imprivata.com). -
Enter a username you associated with administrator access.
The Imprivata Cloud Platform uses the administrator domain to locate your tenant in the cloud.
-
The IdP you configured launches the authentication workflow for this user.
-
After you successfully authenticate, click Launch to open the Imprivata Admin Console without further authentication. If you have any other Imprivata products configured (and this user has access), their admin consoles are also available to launch from this page.
NOTE:When an administrator logs out of the Imprivata Access Management portal, the admin is also logged out of all consoles managed through the portal.